Hi,
By trying to make the audio / video calls work on my matrix-synapse Yunohost server, I realized that there is a lot of misunderstanding about over the different documentations and tutorials that I found online.
A lot of those claim that it is not possible to run a coturn server behind a NAT / VPN, including the official matrix-synapse documentation :
But surprisingly, the coturn official webpage starts with this description :
The TURN Server is a VoIP media traffic NAT traversal server and gateway. It can be used as a general-purpose network traffic TURN server and gateway, too.
NAT traversal ! ! ! !
And, indeed, here is what can be found in the manual of coturn (man coturn in a terminal) :
-X, --external-ip
TURN Server public/private address mapping, **if the server is behind NAT** [...]
I assume that :
- You have matrix-synapse installed on your Yunohost
- Your Yunohost is running behind a VPN hosted on a VPS with a public IP adress
If yes, we are going to :
- Activate this option on our Yunohost
- Forward the right ports on our VPS
1 - On your Yunohost :
To activate the option on your Yunohost, you should edit the conf file /etc/matrix-synapse/coturn.conf
And add or edit this line :
external-ip=XXX.XXX.XXX.XXX/YYY.YYY.YYY.YYY
Where :
XXX.XXX.XXX.XXX is my public IP
YYY.YYY.YYY.YYY is the private ip of your yunohost on the VPN Subnet (Usually something like 10.8.0.x )
EDIT 15/07/2022
It somehow stopped working after I rebooted my Yunohost once.
I spent some time and increased frustration to understand what was going on… And made it work by using the domain name instead of the public IP :
mydomain.com is my domain name
YYY.YYY.YYY.YYY is the private ip of your yunohost on the VPN Subnet (Usually something like 10.8.0.x )
Then restart the coturn-synapse service :
systemctl restart coturn-synapse.service
2 - On your VPN / VPS :
You have to forward from the public static IP network interface to the private IP of the Yunohost on the VPN network subnet the following ports :
- 5349 and 5350 (both TCP and UDP)
- The range of ports from 49153 to 49193 (both TCP and UDP) :
Use the following command, that you’d have to adjust assuming that :
eth0 is the interface of the static public IP of your VPS
tun0 is the interface of your VPN network on your VPS
10.8.0.1 is the private ip of your VPS on the VPN Subnet
10.8.0.2 is the private ip of your yunohost on the VPN Subnet
iptables -A FORWARD -i eth0 -o tun0 -p tcp -m tcp --dport 5349 --tcp-flags FIN,SYN,RST,ACK SYN -m conntrack --ctstate NEW -j ACCEPT
iptables -A PREROUTING -i eth0 -p tcp -m tcp --dport 5349 -j DNAT --to-destination 10.8.0.2
iptables -A POSTROUTING -d 10.8.0.2/32 -o tun0 -p tcp -m tcp --dport 5349 -j SNAT --to-source 10.8.0.1
iptables -A FORWARD -i eth0 -o tun0 -p tcp -m tcp --dport 5350 --tcp-flags FIN,SYN,RST,ACK SYN -m conntrack --ctstate NEW -j ACCEPT
iptables -A PREROUTING -i eth0 -p tcp -m tcp --dport 5350 -j DNAT --to-destination 10.8.0.2
iptables -A POSTROUTING -d 10.8.0.2/32 -o tun0 -p tcp -m tcp --dport 5350 -j SNAT --to-source 10.8.0.1
iptables -A FORWARD -i eth0 -o tun0 -p tcp -m tcp --dport 49153:49193 --tcp-flags FIN,SYN,RST,ACK SYN -m conntrack --ctstate NEW -j ACCEPT
iptables -A PREROUTING -i eth0 -p tcp -m tcp --dport 49153:49193 -j DNAT --to-destination 10.8.0.2
iptables -A PREROUTING -i eth0 -p udp -m udp --dport 49153:49193 -j DNAT --to-destination 10.8.0.2
iptables -A POSTROUTING -d 10.8.0.2/32 -o tun0 -p tcp -m tcp --dport 49153:49193 -j SNAT --to-source 10.8.0.1
iptables -A POSTROUTING -d 10.8.0.2/32 -o tun0 -p udp -m udp --dport 49153:49193 -j SNAT --to-source 10.8.0.1
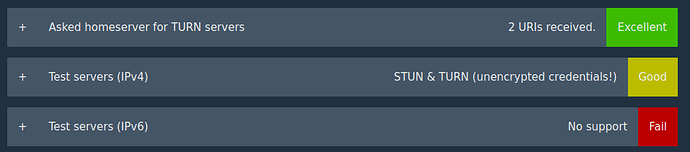
It should now work.
Enjoy !