Mon serveur YunoHost 11
Matériel: VM sur FreeBox Delta
Système d’exploitation: Linux 5.10.0-22-arm64 aarch64
Version de YunoHost: 11.1.0.18 sur Debian 11
Nextcloud version : 25
J’ai accès à mon serveur :** En SSH | Par la webadmin
Êtes-vous dans un contexte particulier ou avez-vous effectué des modifications particulières sur votre instance ?** : non
https://paste.yunohost.org/raw/ogolinuser
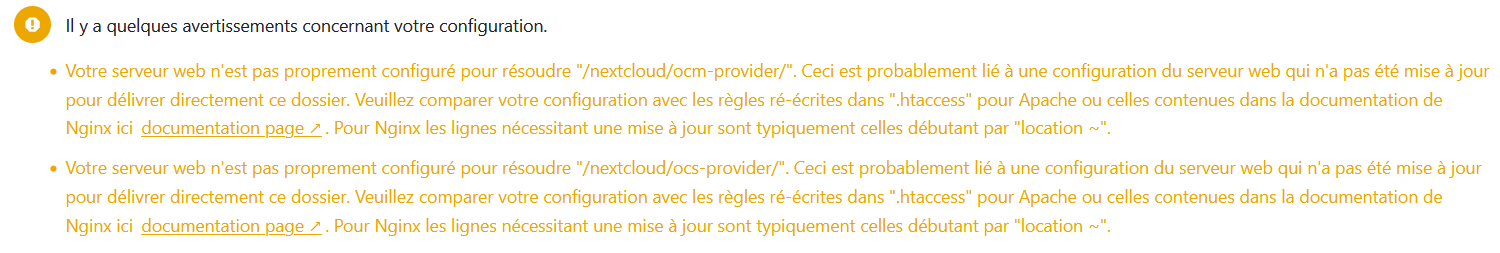
J’ai effectué l’Upgrade de Nextcloud 25 vers 26.0.2, depuis quand j’ouvre la Wenadmin de Nextcloud j’ai ce message d’erreur :
Je suis renvoyé vers cette documentation :
https://docs.nextcloud.com/server/26/admin_manual/installation/nginx.html
Mais je ne vois pas ce qu’il y a d’incorrect.
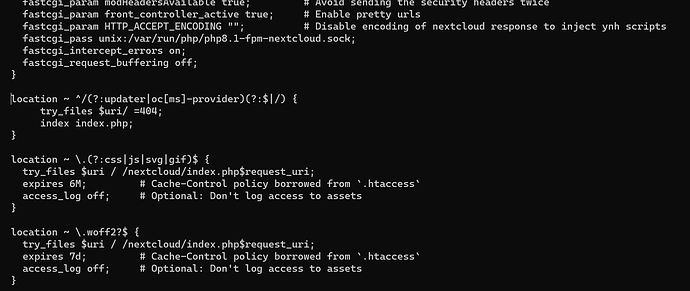
Voici mon nginx :
https://paste.yunohost.org/vuyirafaqo
location ^~ /.well-known {
The following 6 rules are borrowed from
.htaccessThe following 2 rules are only needed for the user_webfinger app.
Uncomment it if you’re planning to use this app.
#rewrite ^/.well-known/host-meta.json /nextcloud/public.php?service=host-meta-json last;
#rewrite ^/.well-known/host-meta /nextcloud/public.php?service=host-meta last;
location = /.well-known/carddav { return 301 /nextcloud/remote.php/dav/; }
location = /.well-known/caldav { return 301 /nextcloud/remote.php/dav/; }
location = /.well-known/webfinger { return 301 /nextcloud/index.php$uri; }
location = /.well-known/nodeinfo { return 301 /nextcloud/index.php$uri; }
try_files $uri $uri/ =404;
}
rewrite ^/nextcloud$ /nextcloud/ permanent;
location ^~ /nextcloud/ {Path to source
alias /var/www/nextcloud/;
Add headers to serve security related headers
more_set_headers “Strict-Transport-Security: max-age=15768000; includeSubDomains; preload;”;
more_set_headers “Referrer-Policy: no-referrer”;
more_set_headers “X-Content-Type-Options: nosniff”;
more_set_headers “X-Download-Options: noopen”;
more_set_headers “X-Frame-Options: SAMEORIGIN”;
more_set_headers “X-Permitted-Cross-Domain-Policies: none”;
more_set_headers “X-Robots-Tag: noindex, nofollow”;
more_set_headers “X-XSS-Protection: 1; mode=block”;Set max upload size
client_max_body_size 10G;
fastcgi_buffers 64 4K;Enable gzip but do not remove ETag headers
gzip on;
gzip_vary on;
gzip_comp_level 4;
gzip_min_length 256;
gzip_proxied expired no-cache no-store private no_last_modified no_etag auth;
gzip_types application/atom+xml application/javascript application/json application/ld+json application/manifest+json>Pagespeed is not supported by Nextcloud, so if your server is built
with the
ngx_pagespeedmodule, uncomment this line to disable it.#pagespeed off;
Remove X-Powered-By, which is an information leak
fastcgi_hide_header X-Powered-By;
Specify how to handle directories – specifying
/nextcloud/index.php$request_urihere as the fallback means that Nginx always exhibits the desired behaviour
when a client requests a path that corresponds to a directory that exists
on the server. In particular, if that directory contains an index.php file,
that file is correctly served; if it doesn’t, then the request is passed to
the front-end controller. This consistent behaviour means that we don’t need
to specify custom rules for certain paths (e.g. images and other assets,
/updater,/ocm-provider,/ocs-provider), and thus
try_files $uri $uri/ /nextcloud/index.php$request_urialways provides the desired behaviour.
index index.php index.html /nextcloud/index.php$request_uri;
Rule borrowed from
.htaccessto handle Microsoft DAV clientslocation = /nextcloud/ {
if ( $http_user_agent ~ ^DavClnt ) {
return 302 /nextcloud/remote.php/webdav/$is_args$args;
}
}
location = /nextcloud/robots.txt {
allow all;
log_not_found off;
access_log off;
}Rules borrowed from
.htaccessto hide certain paths from clientslocation ~ ^/nextcloud/(?:build|tests|config|lib|3rdparty|templates|data)(?:$|/) { return 404; }
location ~ ^/nextcloud/(?:.|autotest|occ|issue|indie|db_|console) { return 404; }Ensure this block, which passes PHP files to the PHP process, is above the blocks
which handle static assets (as seen below). If this block is not declared first,
then Nginx will encounter an infinite rewriting loop when it prepends
/nextcloud/index.phpto the URI, resulting in a HTTP 500 error response.location ~ .php(?:$|/) {
# Required for legacy support
# https://github.com/nextcloud/documentation/pull/2197#issuecomment-721432337
# This line fix the ldap admin page
rewrite ^/nextcloud/(?!index|remote|public|cron|core/ajax/update|status|ocs/v[12]|updater/.+|oc[ms]-provider/.> fastcgi_split_path_info ^(.+?.php)(/.*)$;
set $path_info $fastcgi_path_info;
try_files $fastcgi_script_name =404;
include fastcgi_params;
fastcgi_param SCRIPT_FILENAME $request_filename;
fastcgi_param PATH_INFO $path_info;
fastcgi_param HTTPS on;
fastcgi_param modHeadersAvailable true; # Avoid sending the security headers twice
fastcgi_param front_controller_active true; # Enable pretty urls
fastcgi_param HTTP_ACCEPT_ENCODING “”; # Disable encoding of nextcloud response to inject ynh scripts
fastcgi_pass unix:/var/run/php/php8.1-fpm-nextcloud.sock;
fastcgi_intercept_errors on;
fastcgi_request_buffering off;
}
location ~ .(?:css|js|svg|gif)$ {
try_files $uri / /nextcloud/index.php$request_uri;
expires 6M; # Cache-Control policy borrowed from.htaccess
access_log off; # Optional: Don’t log access to assets
}
location ~ .woff2?$ {
try_files $uri / /nextcloud/index.php$request_uri;
expires 7d; # Cache-Control policy borrowed from.htaccess
access_log off; # Optional: Don’t log access to assets
}
location ~ / {
if ($request_method ~ ^(PUT|DELETE|PATCH)$) {
rewrite ^ /nextcloud/index.php$request_uri last;
}
try_files $uri / /nextcloud/index.php$request_uri;
}show YunoHost panel access
include conf.d/yunohost_panel.conf.inc;
}
Quelqu’un pourrait-il m’aider ? Merci ![]()