Can anyone here tell if YNH servers are vulnerable to the Log4Shell zeroday?
This is an apache utility, yunohost uses nginx.
Apache Log4j is a Java-based logging utility. It was originally written by Ceki Gülcü and is part of the Apache Logging Services project of the Apache Software Foundation. Log4j is one of several Java logging frameworks.
(I may be wrong)
I never heard about Log4j before today, so I guess nope
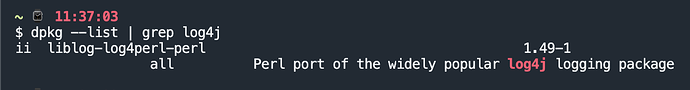
You can convince yourself with dpkg --list | grep log4j
It is an apache utility, but the way I understand it, Apache here is more like the foundation’s name (similar to the ‘GNU’ in Gimp / GNU image processor) than an actual relation to Apache web server ![]()
Thnx for the quick response and providing relief!
I was wrong. This is affecting a lot of Web apps. Its team is working nonstop to get a patch.
What might be vulnerable is some packaged app dependency or similar. If one of them use that software, that might be an issue.
“Like many projects, Log4j is only maintained by volunteers, and because of this, coordination of security response is naturally more difficult: a coordinated embargo is easy to coordinate, if you have a dedicated maintainer to do it. In the absence of a dedicated maintainer, you have chaos: as soon as a commit lands in git to fix a bug, the race is on: security maintainers are scurrying to reverse engineer what the bug you fixed was, which is why vulnerability embargoes can be helpful.”
FROM: Security Alert: Apache Log4j Zero Day Exploit | Tux Machines
I hope the yuno team can find a solution specially if some apps use this as a dependency! Looks scary for the big guys …
Minecraft server app seems to be affected. I have updated the package, but user will have to manually upgrade as the package isn’t on the app catalog.
I had a perl port of log4j on one of my servers, i removed it by security. My other servers hadn’t log4j installed.
I confirm a Perl port of log4j
It seems to be linked to Munin.
Not sure it’s affected but as I don’t really use Munin anymore, it won’t hurt removing it (and Munin alongside).
I’m seeing a lot of attempts to exploit this vuln on my public instance (over 50 in the last 48 hrs).
Thankfully, someone developed a quick python utility (with no dependencies other than python3) to check the logs of your server just in case : GitHub - Neo23x0/log4shell-detector: Detector for Log4Shell exploitation attempts
Unfortunately, the assessment of potential affected packages is difficult since log4j could be included in so many apps…
Edit: you can also run these commands (as admin or root) to check if you’re affected (source: github repo linked above)
sudo ps aux | egrep '[l]og4j'
sudo find / -iname "log4j*" 2>&1 | grep -v "Permission denied"
sudo lsof | grep log4j
Edit 2: You can also check the following resource put together by the NCSC (Dutch CISA) to check if you’re running software identified as vulnerable:
For french admins, there is an french translation of readme of log4Shell-detector : Log4shell-detector — OSWiki
Pour les admins francophones, il y a une traduction française du readme de log4Shell-detector : Log4shell-detector — OSWiki
Found several instances of log4j, all version 1.x.x do these versions share the same vulnerabilities?
/usr/share/java/log4j-1.2-1.2.17.jar
/usr/share/maven-repo/log4j/log4j/1.2.17/log4j-1.2.17.jar
/usr/share/maven-repo/org/slf4j/log4j-over-slf4j/1.7.25/log4j-over-slf4j-1.7.25.jar
Hi everyone,
For French-speaking admins, you might want to try that :