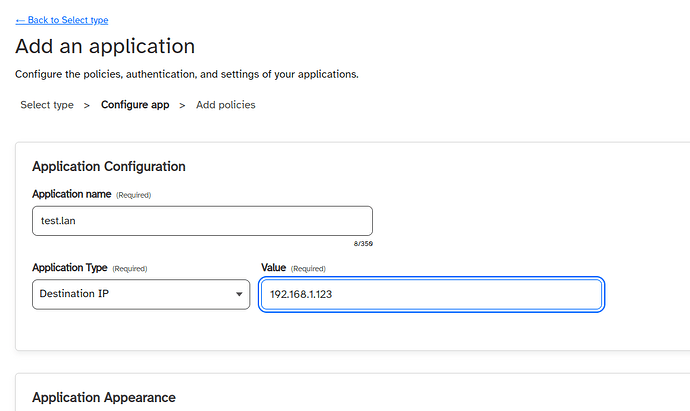
Well here is my config
cat /etc/cloudflared/default.yml
tunnel: default
credentials-file: /root/.cloudflared//xxxxxxxxxxxxx.json
ingress:
- hostname: yuno.example.dev
originRequest:
connectTimeout: 10s
disableChunkedEncoding: true
service: https://localhost:443
- hostname: jf.example.dev
originRequest:
connectTimeout: 10s
disableChunkedEncoding: true
service: https://localhost:443
- hostname: jf2.example.dev
originRequest:
connectTimeout: 10s
disableChunkedEncoding: true
service: https://localhost:8095
- service: hello_world
logfile: /var/log/cloudflared_default.log
no-tls-verify: True
loglevel: warn
I remove logfile and restart the service
Jul 16 11:12:39 yuno.home systemd[1]: Stopping cloudflared tunnel for default...
Jul 16 11:12:39 yuno.home cloudflared[662336]: 2023-07-16T10:12:39Z ERR Failed to serve quic connection error="context canceled" connIndex=1 event=0 ip=x.x.x.27
Jul 16 11:12:39 yuno.home cloudflared[662336]: 2023-07-16T10:12:39Z ERR Failed to serve quic connection error="context canceled" connIndex=3 event=0 ip=x.x.x.63
Jul 16 11:12:39 yuno.home cloudflared[662336]: 2023-07-16T10:12:39Z ERR Failed to serve quic connection error="context canceled" connIndex=2 event=0 ip=x.x.x.7
Jul 16 11:12:39 yuno.home cloudflared[662336]: 2023-07-16T10:12:39Z ERR Failed to serve quic connection error="context canceled" connIndex=0 event=0 ip=x.x.x.43
Jul 16 11:12:39 yuno.home cloudflared[662336]: 2023-07-16T10:12:39Z ERR no more connections active and exiting
Jul 16 11:12:39 yuno.home cloudflared[662336]: 2023-07-16T10:12:39Z ERR icmp router terminated error="context canceled"
Jul 16 11:12:39 yuno.home systemd[1]: cloudflared@default.service: Succeeded.
Jul 16 11:12:39 yuno.home systemd[1]: Stopped cloudflared tunnel for default.
Jul 16 11:12:39 yuno.home systemd[1]: Started cloudflared tunnel for default.
While using https for service I get
{"level":"error","event":0,"ip":"x.x.x.57","connIndex":1,"error":"context canceled","time":"2023-07-16T10:18:31Z","message":"Failed to serve quic connection"}
{"level":"error","event":0,"ip":"x.x.x.27","connIndex":2,"error":"Application error 0x0 (remote)","time":"2023-07-16T10:18:31Z","message":"Failed to serve quic connection"}
{"level":"error","event":0,"ip":"x.x.x.27","connIndex":2,"error":"Application error 0x0 (remote)","time":"2023-07-16T10:18:31Z","message":"Serve tunnel error"}
{"level":"error","time":"2023-07-16T10:18:31Z","message":"writing finish: Application error 0x0 (remote)"}
{"level":"error","event":0,"ip":"x.x.x.53","connIndex":3,"error":"Application error 0x0 (remote)","time":"2023-07-16T10:18:31Z","message":"Failed to serve quic connection"}
{"level":"error","event":0,"ip":"x.x.x.53","connIndex":3,"error":"Application error 0x0 (remote)","time":"2023-07-16T10:18:31Z","message":"Serve tunnel error"}
{"level":"error","event":0,"ip":"x.x.x.33","connIndex":0,"error":"context canceled","time":"2023-07-16T10:18:31Z","message":"Failed to serve quic connection"}
{"level":"error","time":"2023-07-16T10:18:31Z","message":"no more connections active and exiting"}
{"level":"error","error":"context canceled","time":"2023-07-16T10:18:31Z","message":"icmp router terminated
While using http, the log file is empty.
![]()
![]()
![]()